How zero-trust BPO data management governs every aspect of how our agents access, use, and are prevented from misusing the sensitive subscriber data entrusted to us by carrier partners.
When a carrier outsources customer support, billing, or fraud operations to a BPO, they are entrusting that partner with their most sensitive asset: subscriber data. Names, addresses, SSNs, payment information, call records, and account credentials flow through BPO systems and are visible to BPO agents. The security question is not whether the BPO has firewalls. It is whether every individual agent interaction with subscriber data is governed, monitored, and controlled to prevent both external breach and internal misuse.
Zero-trust BPO data managementis Sequential Tech’s comprehensive approach to protecting the subscriber data our agents handle. Zero-trust means no agent, system, or process is inherently trusted. Every data access is authenticated, authorized, logged, and monitored. Every agent’s access is limited to the minimum data required for their specific task. Every anomalous access pattern triggers investigation. This is not a technology policy — it is an operational culture that governs how every person in our organization interacts with client data.
How Zero-Trust Governs Agent Data Access
Zero-Trust Controls at Every Agent Interaction Point
|
Control Point |
Zero-Trust Measure |
What It Prevents |
How It Is Monitored |
|---|---|---|---|
|
Agent authentication |
Multi-factor authentication at every login, session timeout after inactivity |
Unauthorized access using shared or compromised credentials |
Login anomaly detection: unusual times, locations, devices |
|
Role-based data access |
Agent sees only the data fields required for their specific function |
Billing agents seeing fraud data, collections agents seeing full SSN unnecessarily |
Access audits verify each role sees only permitted data fields |
|
Screen recording and monitoring |
All agent screens recorded and available for random and triggered audit |
Agents photographing screens, copying data to personal devices or notes |
AI-powered screen monitoring flags unauthorized application access |
|
Data export restrictions |
No USB, no personal email, no cloud storage access from agent workstations |
Bulk data extraction via external media or personal accounts |
DLP (Data Loss Prevention) systems block and log all export attempts |
|
Clean desk and clean screen policy |
No paper, no personal devices at workstations; screens lock automatically |
Physical data capture via photos, handwritten notes, or screen observation |
Physical security checks, random workstation audits, CCTV monitoring |
Agent Training: Security as Culture, Not Just Compliance
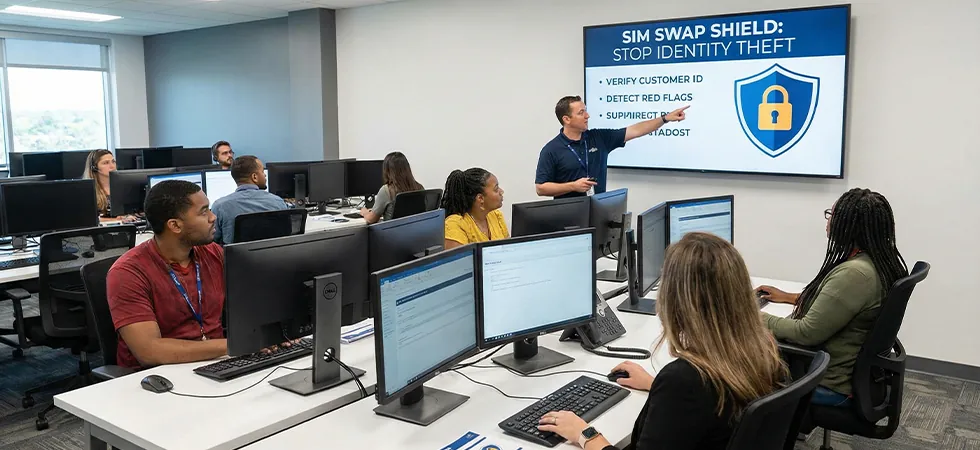
Zero-trust BPO data managementrequires agents who understand not just the rules but the reasons behind them. Sequential Tech’s security training goes beyond policy recitation to build genuine security awareness. Agents learn why subscriber data is valuable to criminals, how data breaches occur in BPO environments, what specific behaviors put data at risk, and what their personal accountability is for the data they handle. This training transforms security from a checkbox requirement into an operational mindset.
Refresher training occurs quarterly, incorporating real-world breach case studies (anonymized) from the BPO industry. Agents who demonstrate exemplary security awareness are recognized. Agents who violate data handling policies face immediate consequences proportional to the severity of the violation. This combination of education, recognition, and accountability creates the security culture that policy documents alone cannot achieve.
“Zero-trust is not a technology stack. It is a belief system: nobody is trusted by default, and everyone earns trust through verified behavior. In a BPO handling millions of subscriber records, that belief system must permeate every agent interaction, every workstation configuration, and every access decision. Technology enforces the controls. Culture makes people follow them willingly.” — BPO Data Security Report, 2026
Client Transparency: Proving Security, Not Just Claiming It
Sequential Tech provides carrier clients with full transparency into our security posture: SOC 2 Type II certification, regular penetration testing results, access audit reports, incident response documentation, and real-time dashboards showing security compliance metrics. Carrier clients can verify at any time that the zero-trust controls governing their subscriber data are functioning as promised. This transparency is not a vulnerability; it is the foundation of the trust that makes outsourcing viable.
TRUST US WITH YOUR DATA BECAUSE WE DON’T TRUST OURSELVES BY DEFAULT
Sequential Tech’s zero-trust BPO data management governs every agent interaction with subscriber data through authentication, access control, monitoring, and a security culture that protects what carriers entrust to us.