How a SIM swap fraud prevention strategy depends on trained call center agents who recognize social engineering cues, follow verification protocols, and serve as the last line of defense against the #1 account takeover threat of 2026.
SIM swap fraud is devastatingly effective because it exploits the weakest link in telecom security: the human interaction. A fraudster calls the carrier’s support line, impersonates the subscriber, and convinces an agent to transfer the phone number to a new SIM. With that number, they intercept two-factor authentication codes, access banking apps, compromise email accounts, and drain financial assets, often within minutes. The technology to detect suspicious swap patterns exists. But the most critical intervention point is the agent on the phone who decides whether to process the swap or flag it for investigation.
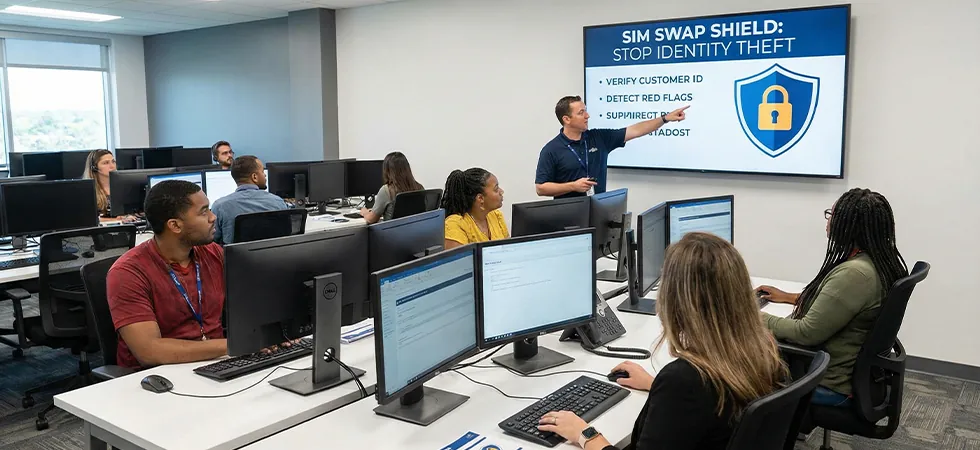
A SIM swap fraud prevention strategy begins and ends with the agents handling swap requests. ML systems can score risk in the background, but it is the agent who asks the probing questions, recognizes the social engineering script, and makes the real-time decision to verify, delay, or refuse a suspicious request. Sequential Tech trains and deploys the fraud-aware agents who serve as the human shield between social engineers and subscriber identities.
How Social Engineers Manipulate Untrained Agents
Social Engineering Tactics and Trained Agent Countermeasures
|
Social Engineering Tactic |
What the Fraudster Says |
Untrained Agent Response |
Trained Agent Countermeasure |
|---|---|---|---|
|
Urgency pressure |
“I’m overseas, my phone was stolen, I need this done NOW” |
Rushes to help, skips verification steps out of empathy |
Follows full protocol regardless of urgency; urgency itself is a red flag |
|
Authority claim |
“I’m calling from the fraud department” or drops manager names |
Defers to perceived authority, processes without question |
Verifies through internal channels; no external caller has override authority |
|
Personal detail flooding |
Recites SSN last four, DOB, address from breached databases |
Accepts data breach info as proof of identity |
Recognizes that static data can be purchased; uses dynamic verification questions |
|
Emotional manipulation |
“My daughter is sick, I need my phone to contact her doctor” |
Lets sympathy override protocol |
Empathetic but firm; offers alternative resolution without bypassing verification |
|
Repeated callback pattern |
Calls multiple times, getting different agents, hoping one will comply |
Each agent treats it as a new request, unaware of previous denials |
Account flagging system alerts agent to prior swap attempts and denials |
Training Agents as the Last Line of Defense
A SIM swap fraud prevention strategy at Sequential Tech includes three training layers for every agent who handles swap requests. First, social engineering recognition: agents learn the specific scripts, emotional triggers, and pressure tactics that fraudsters use, so they can identify an attack in real time rather than recognizing it in hindsight. Second, verification protocol mastery: agents follow a mandatory multi-step verification process that goes beyond static data (SSN, DOB) to include dynamic challenges the real subscriber can answer but a fraudster cannot. Third, escalation confidence: agents are trained and empowered to delay or refuse suspicious requests without fear of customer complaints or management pushback.
“Every SIM swap that a fraudster completes went through an agent who could have stopped it. The agent who recognizes social engineering, follows verification protocols, and has the confidence to say no to a convincing impersonator is the most valuable fraud prevention asset a carrier has. No algorithm replaces that human judgment in real time.” — Telecom Fraud Prevention Report, 2026
The Agent-ML Partnership: Risk Scoring Meets Human Judgment
Sequential Tech’s agents work alongside ML-powered risk scoring systems that flag suspicious swap patterns in the background: unusual device history, geographic anomalies, recent account changes, or rapid successive swap attempts. When the ML system elevates a risk score, the agent sees a visual alert and escalates to enhanced verification. But the agent also catches the cases ML misses, the socially engineered request that appears normal in the data but sounds wrong on the phone. The combination of algorithmic scoring and human intuition catches fraud that neither could catch alone.
TRAIN YOUR AGENTS TO STOP SIM SWAP FRAUD AT THE POINT OF CONTACT
Sequential Tech’s fraud-aware agents recognize social engineering, follow rigorous verification, and serve as the human shield that prevents account takeover.