How VoIP fraud prevention services depend on trained fraud analysts and support agents who investigate suspicious account activity, validate caller identity through multi-channel verification, and respond to abuse patterns that automated systems flag but cannot resolve alone.
VoIP services are disproportionately targeted by fraudsters because digital voice accounts are easier to create, harder to trace, and simpler to abuse than traditional phone lines. Account creation fraud, toll fraud, robocall origination, caller ID spoofing, and service abuse generate billions in annual losses. Automated detection systems flag suspicious patterns, but the investigation, identity validation, and abuse resolution require human analysts and agents who can make judgment calls that algorithms cannot.
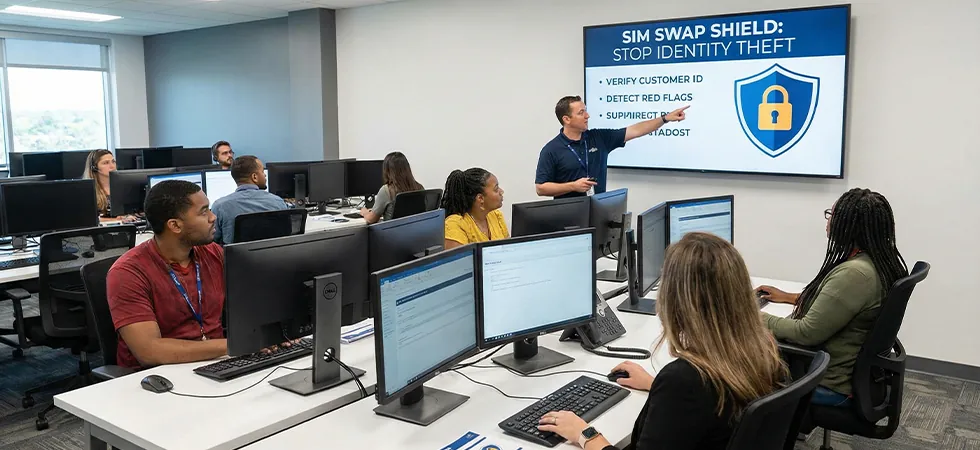
VoIP fraud prevention servicescombine automated flagging with human investigation, validation, and response. Sequential Tech provides the fraud analysts who investigate flagged accounts, the support agents who verify legitimate users caught in fraud filters, and the abuse response teams who shut down confirmed bad actors before they generate significant damage.
VoIP Fraud Types and Agent/Analyst Response
Fraud Categories and Human Response Requirements
|
VoIP Fraud Type |
Automated Detection Signal |
Analyst/Agent Investigation |
Resolution Action |
|---|---|---|---|
|
Account creation fraud |
Multiple accounts from same IP, disposable email patterns |
Analyst reviews activation cluster, checks identity documents, assesses pattern |
Suspend fraudulent accounts, whitelist legitimate ones caught in filter |
|
Toll fraud (PBX hijacking) |
Sudden international call volume from enterprise VoIP account |
Agent contacts enterprise client to verify, analyst checks for known PBX exploit patterns |
Restrict international access, assist client with PBX security remediation |
|
Robocall origination |
High-volume outbound with short duration and low answer rates |
Analyst verifies account purpose, checks caller ID legitimacy, reviews content if recorded |
Terminate account, report to industry robocall traceback consortium |
|
Caller ID spoofing |
Outbound calls using caller IDs not assigned to the account |
Analyst traces spoofed numbers, determines intent (malicious vs. misconfigured) |
Block unauthorized caller IDs, educate legitimate users on proper configuration |
|
Service abuse (free tier exploitation) |
Accounts cycling through free trials, generating revenue-share traffic |
Analyst maps account cluster by payment method, device fingerprint, or behavior pattern |
Close fraudulent accounts, implement controls to prevent re-creation |
Protecting Legitimate Users from False Positives
VoIP fraud prevention servicesmust balance fraud blocking with legitimate user protection. Aggressive automated filters inevitably catch some genuine users: a small business making legitimate high-volume international calls, a new account that triggers creation fraud patterns due to VPN usage, or an enterprise whose calling patterns change after a merger. The support agent’s role is to validate these legitimate users quickly, restore their service, and whitelist their accounts to prevent repeated disruption.
Sequential Tech’s agents are trained to handle these sensitive interactions with professionalism and efficiency. The subscriber who has been falsely flagged is frustrated and needs rapid resolution. The agent verifies their identity through enhanced protocols, restores service, documents the false positive, and ensures the fraud system is updated to prevent recurrence. This false-positive recovery is as critical to service quality as the fraud detection itself.
“The fraud prevention system that blocks a legitimate enterprise client’s international calling for six hours has done more damage to the carrier-client relationship than most fraudsters ever could. The human analyst who validates the legitimate user within 15 minutes is protecting both revenue and relationships.” — VoIP Service Operations Report, 2026
BLOCK FRAUD WITHOUT BLOCKING LEGITIMATE USERS
Sequential Tech’s VoIP fraud analysts investigate suspicious activity, validate legitimate users caught in filters, and shut down bad actors; balancing protection with service quality.